This post has two sections, the first section focused on an interest observation on the challenge document. The second focused on solving the challenge.
Anti Forensic Trick
While solving the challenge, I noticed the document could only be executed once. After a single execution, the document failed to work. I also noticed the file size reduced after a single execution.
I went on to investigate why. I noticed the following lines of code.
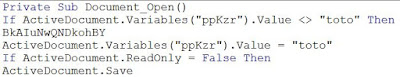
The above macro is executed when the document is open. However, it only proceed to execute the function "BkAIuNwQNDkohBY" only if the variable "ppKzr" is NOT "toto". "BkAIuNwQNDkohBY" contained the key functions of the code. If "BkAIuNwQNDkohBY" is executed, the variable "ppKzr" is overwritten with "toto".
I compared the hexdump of the documents before and after execution.
The long string stored in "ppKzr" was overwritten with "toto" which resulted in the document reducing in size.
With the long string overwritten the document could not be executed. Not only that we would not be able to de-obfuscate the strings in VB code. The long string is used as a dictionary in the de-obfuscation function "QklkhFEQNB". This 'trick' could be used by malware writer to prevent analysis from being done on the document after it is executed.
Solving the challenge
First, I choose to dump the macro using various tools. This blog post by Lenny Zeltster contained a number of the tools. The following diagram showed how I used olevba.
After reading the code I realised many of the strings are obfuscated. Then I made use of the debugging function in Visual Basic for Applications (VBA) in Word 2010. The short cut to activate it is Alt+F11.
After reading the code I realised many of the strings are obfuscated. Then I made use of the debugging function in Visual Basic for Applications (VBA) in Word 2010. The short cut to activate it is Alt+F11.
From the code, the function "QklkhFEQNB" was called many times to de-obfuscate strings. Without going into the details of how the function worked. I used added "MsgBox" to dump out the strings after de-obfuscation was done.
After executing the document, the MsgBox would dump the de-obfuscated strings.
From this URL, we can notice its going to "10.1.33.7". The long string seems to be base64 encoded. Given a clue "b64" from the URL. After decoding the string, it seems like a long string of hex values. Using the next clue "x58". XOR was performed on the string and it decoded into the flag.







how do you access/dump the macro code from a Word doc?
ReplyDeleteThanks!
I have just updated the blogpost in the begining of the section "Solving the Challenge" on how I used olevba to dump the macro from a word doc.
Delete