Key takeaways:
1. Identify the differences between static and virtual functions.
Assumptions
The example code only has a single class and one child class. Both parent and child classes has one virtual function on top of the static ones.
Let me begin with this C++ code:
Explanation on what the above code does
The above code first define a "Animal" class. The "Animal" class contains 3 public variables "name", "food" and "legs". It also has 4 member functions. "Animal()" is the constructor while "~Animal()" is the destructor function. "Naming" is a member function implemented to interact with the "name" variable in the object of "Animal" class. "Eating" is also a member function but its a Virtual function that interact with variable "food".
Next, is the definition of a "Cats" class which is a child class of "Animal".The "Cats" class contains variable "toys" and 4 member functions. "Cats()" is the constructor while "~Cats()" is the destructor function. "Playing" is a member function implemented to interact with the "toys" variable in the object of "Cats" class. "Eating" is also a member function but its a Virtual function that interact with variable "food".
Use of virtual function allows the correct virtual function to be called based on the object type. In this example, the object of class "Animal" would use a different "Eating" function comparing to the one in "Cats". The following shows the output when the above C++ code is executed. Note the output string from "Eating" function for "Animal" object is different from the one for "Cats".

This demonstrate a key concept in OOP, Polymorphism.
Next is the "Cats" class with 1 public variable "toys". It also have constructor and destructor functions. "Playing" is a member function implemented to interact with the "toys" variable in the object of "Cats" class.
Inside the main function, an object "Generic_Animal" of type class "Animal" is created. And its member functions "Naming" and "Eating" are called. Then an object pointed by "pCat1" of type class "Cats" is created. The variables "name" and "food" are overwritten with different strings for the object. Finally, the member functions "Playing" and "Eating" are called.
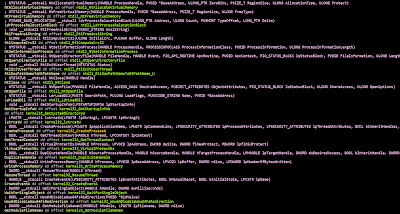
Analysing the compiled version of the above C++ code
Let's begin by looking into the constructor of the "Animal" class

EBX contained the address of the object of type "Animal" class. The first value being initialized is the 'Vftable' or Virtual Function Table. This table contained the address of the virtual functions in the object. In this case its the "Eating" virtual function.
Now we will construct a struct to represent the members in "Animal" class. Take note how the start of the object will be pointer to the Virtual Function table (Vftable) if a virtual function is present.

I will skip over the constructor and struct for "Cats" class. However, if you need help just leave a comment below.
1. Identify the differences between static and virtual functions.
Now, I will go over the difference between static and virtual functions. The following code snipped at the late part of Main().
The first call is made to "FN_Cats_Playing" which is the "Playing" function in "Cats" class. Next, the Virtual Function table of "Cats" class is retrieve and the "Call" instruction is made to the first function in the Vftable. The first function is "Eating" in the object of type "Cats".